Shipping included*
Exclusions
Additional shipping fees may apply in rare circumstances for deliveries outside standard service areas. In most cases, this only potentially affects shipments to the Northwest Territories and Yukon, as well as certain heavy or oversized items.
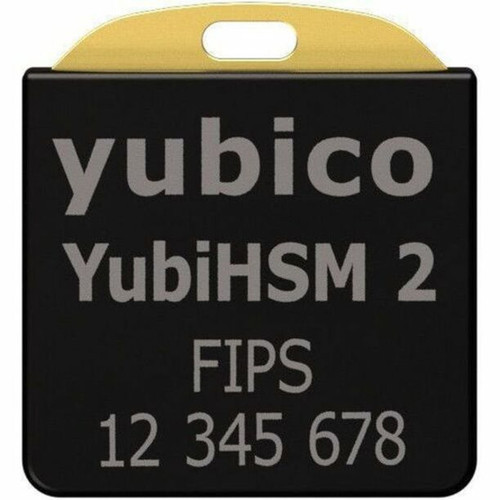
Yubico 8880001127 YubiHSM 2 Security Token - 128-bit - 256-bit - RSA 2048/4096 - SHA-1 Encryption - FIPS 140-2 IP68 - USB Type A
Business volume discounts
Technical guidance
Preparation & staging
QC · ON · AB · BC
Product Features
Technical Overview
The YubiHSM 2 Security Token implements hardware-based cryptographic operations with support for industry-standard algorithms. The token's security architecture is validated through NIST FIPS 140-2 Level 3 certification and IP68 environmental protection rating, ensuring both cryptographic integrity and physical resilience.
This security token connects via USB Type A interface, providing straightforward integration with existing IT infrastructure. The compact form factor measures just 0.47" × 0.51" × 0.12" (12 × 13 × 3.10 mm) and weighs approximately 0.04 oz (1 g), making it highly portable while maintaining enterprise-grade security capabilities.
This section brings together practical product details such as Encryption, Features, USB, USB Standard, so buyers can judge configuration, deployment fit, and day-to-day suitability with less guesswork.
A strong technical summary explains how the product's interfaces, hardware profile, and operating characteristics work together in real deployment. Buyers often need this context to confirm compatibility with existing devices, expected performance in daily use, and whether installation will be straightforward for IT staff or end users.
Key Product Advantages
The YubiHSM 2 Security Token delivers hardware-based security with multiple advantages for business authentication and cryptographic operations.
These strengths make the product easier to deploy and manage in real environments, especially where reliability, usability, and day-to-day operational continuity matter. Notable benefits include Hardware Security Module, Enterprise Durability, Compliance Ready.
Hardware Security Module
Provides dedicated cryptographic processing in tamper-resistant hardware, isolating sensitive operations from host system vulnerabilities.
- Hardware-based key storage
- Tamper-resistant design
- Isolated cryptographic processing
Enterprise Durability
Built to withstand demanding environments with water resistance and crush resistance features.
- IP68 environmental protection
- Physical damage resistance
- Industrial-grade construction
Compliance Ready
Certified to NIST FIPS 140-2 standards and compliant with environmental regulations including WEEE and RoHS directives.
- FIPS 140-2 validated
- Regulatory compliance
- Environmental standards
Deployment / Use Cases
The YubiHSM 2 Security Token is designed for deployment scenarios requiring hardware-based cryptographic security and authentication. Its compact form factor and USB connectivity make it suitable for both fixed installations and mobile security applications.
Common deployment scenarios include secure authentication for network access, cryptographic key management for digital signatures, hardware-based encryption for sensitive data, and secure boot processes for critical systems. The token's FIPS 140-2 certification makes it appropriate for government, financial, and healthcare applications with strict security requirements.
This section brings together practical product details such as Encryption, Features, USB, USB Standard, so buyers can judge configuration, deployment fit, and day-to-day suitability with less guesswork.
Deployment planning benefits from clear examples of where the product fits best, how it may be installed or used, and which business scenarios it supports most naturally. This helps teams judge whether the product belongs at a fixed desk, in a shared workspace, in a meeting area, or as part of a broader managed device rollout.
Physical Profile
The YubiHSM 2 Security Token features an ultra-compact design measuring just 0.47" in height, 0.51" in width, and 0.12" in depth (12 × 13 × 3.10 mm). With a weight of approximately 0.04 oz (1 g), this token is highly portable while maintaining robust construction with water-resistant and crush-resistant properties. The IP68 rating ensures protection against dust ingress and prolonged immersion in water, making it suitable for various environmental conditions.
- Width
- 0.51" (13 mm)
- Depth
- 0.12" (3.10 mm)
- Height
- 0.47" (12 mm)
- Weight
- 0.04 oz (1 g)
Highlights
- Hardware security module with dedicated cryptographic processing
- Supports 128-bit, 256-bit, RSA 2048-bit, and RSA 4096 encryption
- SHA-1 hashing algorithm implementation
- NIST FIPS 140-2 Level 3 certified security
- IP68 rated for water and dust resistance
- Crush-resistant construction for durability
- USB Type A connectivity for easy integration
- Compliant with WEEE and RoHS environmental standards
- Ultra-compact dimensions: 0.47" × 0.51" × 0.12"
- Lightweight design at approximately 0.04 oz (1 g)
Specifications
| Specifications | |
|---|---|
| Manufacturer | Yubico |
| Manufacturer Part Number | 8880001127 |
| Brand Name | Yubico |
| Product Line | YubiHSM 2 |
| Product Name | YubiHSM 2 Security Token |
| Product Type | Security Token |
| Technical Information | |
| Encryption | 128-bit,256-bit,RSA 2048-bit,RSA 4096,SHA-1 |
| Features | Water Resistant,Crush Resistant |
| Interfaces/Ports | |
| USB | Yes |
| USB Standard | USB Type A |
| Physical Characteristics | |
| Height | 0.47" (12 mm) |
| Width | 0.51" (13 mm) |
| Depth | 0.12" (3.10 mm) |
| Weight (Approximate) | 0.04 oz (1 g) |
| Miscellaneous | |
| Certifications & Standards | NIST - FIPS 140-2 IP68 NIST SP800-63B |
| Environmental Compliance | Waste Electrical and Electronic Equipment Directive (WEEE),Restriction of Hazardous Substances (RoHS) |
User Manual
FAQ
What encryption standards does the YubiHSM 2 Security Token support?
The YubiHSM 2 Security Token supports multiple encryption standards including symmetric 128-bit and 256-bit algorithms, RSA 2048-bit and 4096-bit public key cryptography, and SHA-1 hashing. This comprehensive encryption support enables various cryptographic operations including encryption, decryption, digital signatures, and secure hashing within the hardware security module.
What certifications does this security token have?
This security token is certified to NIST FIPS 140-2 Level 3 standards, validating its cryptographic security implementation. It also carries an IP68 environmental protection rating for dust and water resistance. Additionally, the product complies with environmental regulations including the Waste Electrical and Electronic Equipment Directive (WEEE) and Restriction of Hazardous Substances (RoHS) directives.
How does the YubiHSM 2 connect to systems?
The YubiHSM 2 Security Token connects via USB Type A interface, providing straightforward integration with computers and other devices supporting USB connectivity. This standard interface ensures compatibility with most modern IT infrastructure without requiring specialized ports or adapters for deployment.
What physical durability features does this token offer?
The YubiHSM 2 Security Token features water-resistant and crush-resistant construction. The IP68 rating certifies protection against dust ingress and prolonged immersion in water up to specified depths. These durability features make the token suitable for various environmental conditions and help protect against physical damage in demanding deployment scenarios.
What are the dimensions and weight of this security token?
The YubiHSM 2 Security Token measures 0.47 inches in height, 0.51 inches in width, and 0.12 inches in depth (12 × 13 × 3.10 millimeters). It weighs approximately 0.04 ounces (1 gram), making it an ultra-compact and lightweight hardware security solution that's highly portable while maintaining robust security capabilities.
What are typical use cases for this hardware security module?
Typical use cases include secure authentication for network and system access, cryptographic key management for digital signatures and certificates, hardware-based encryption for sensitive data protection, and secure boot processes for critical systems. The FIPS 140-2 certification makes it suitable for government, financial, healthcare, and other regulated environments requiring validated cryptographic security.
What connectivity or interface options are available?
Connectivity support is listed in the product specifications, including the relevant wireless or port options when available.